 We’ve all sent emails at some point that were either better left unsent, or were intended for a different recipient. With Gmail’s new Undo Send feature, you now have the power to transcend the depths of time and space to take back your thoughts… within approximately 30 seconds, that is. It’s a race against time. Are you up to the challenge?
We’ve all sent emails at some point that were either better left unsent, or were intended for a different recipient. With Gmail’s new Undo Send feature, you now have the power to transcend the depths of time and space to take back your thoughts… within approximately 30 seconds, that is. It’s a race against time. Are you up to the challenge?
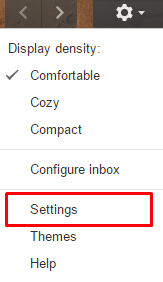
This feature has been an experimental add-on for quite some time, but it has since become an official feature of Gmail. To make things even better, it’s super easy to activate and use. All you have to do is click Settings in the top location of your Gmail inbox (under the gear button).
Next, you’ll want to scroll halfway down the page. Find the Undo Send setting. This is what you’re looking for.
![]()
Once you find it, you want to check the box, Enable Undo Send. There’s also a drop-down menu that gives you the choice of between 5, 10, 20, and 30 seconds where you’ll be able to take back your messages. If you tend to hesitate, the full 30 seconds will provide you with the maximum time required to make up your mind. Just make sure to click Save All Changes before giving it a shot.
Next time you send an email that might be somewhat unsavory, or to the completely wrong user, click Undo at the top of the mailbox. Keep in mind that if you wait too long, your message will be sent. If anything, it’s merely a safeguard against sending anything too salty for your work account. A lot of the time, the kinds of messages you want to take back are ones that can more easily be addressed in person or over the phone.
For more great tips from Voyage Technology, check back with our blog next week.


